All this awareness would make us liable. Without them its ignorance, if we hire them it becomes negligence and I prefer ignorance.
RyanSepe
February 28, 2020
Suggested caption to this cartoon:
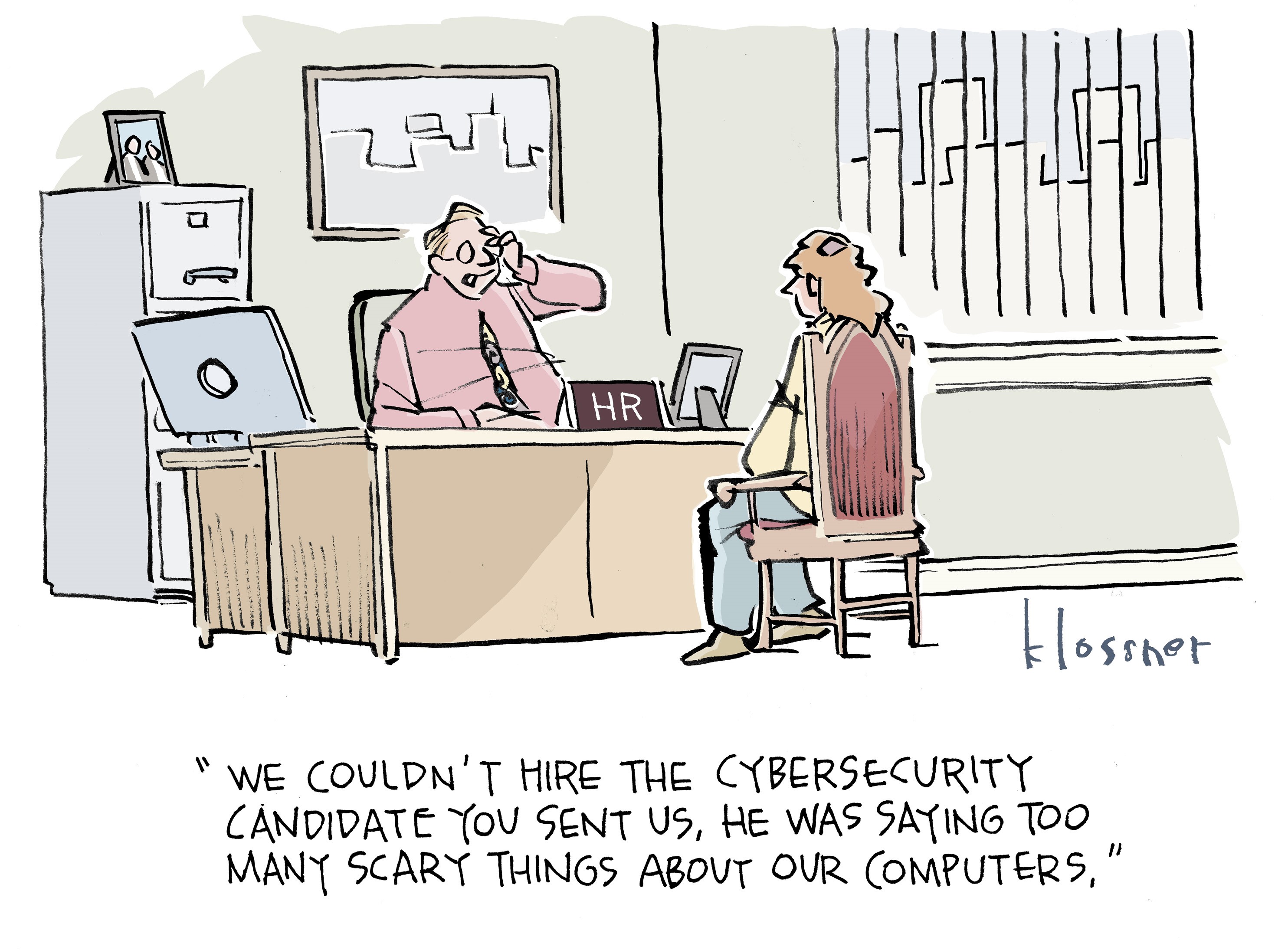
[There is way too much truth in this.
Companies have finite resources. They have to prioritize their cyber security efforts. If something is documented as an active issue, or even a potential weakness, and they don’t address it in a timely manner they have legal liability issues to deal with as well as fixing the problem.
In the “big picture” view of things companies have a lot of motivation to “not put it in writing” until they have the resources to deal with it. On the other hand, if managers don’t show they have a backlog and are overworked they aren’t going to get the resources to fix things in a timely manner. I have more than a little sympathy for cyber security managers caught in this dilemma.
After illegal computer access incidents have been made public Barb sometimes tells me, “I wish they would just stop doing that!” I would be out of a job, but the world would be a better place. So much money is spent on security that from a big picture you see it as huge waste of human and even natural resources (millions of computers monitor and guard against intrusion as their sole purpose). Even when the criminals are caught (extremely rare) they will never have to pay for all the resources spent in finding them and bringing them to justice.
And, of course, it’s never going to happen. Some of these criminals do it for the “free” money. Others do it for the thrill. And some do because they are spies in search of information useful to their country. There are always going to be those type of people. The best we can do is find them, stop them, and prosecute them if we can build a case against them.—Joe]

This reminds me of U-Haul’s infamous “dumb shit memo” which instructs managers to plead ignorance in order to deflect liability.
Closer to topic, ignorance should not protect the entire corporate C-suite from the consequences of leaving PII in an unsecured AWS data bucket.
Would it be feasible to track down the people who design and distribute malware, if there was sufficient money to fund the hunt, and pay the hit team to take them out?
I’m thinking this could be crowdfunded. Eventually, with enough dead bodies scattered around the world, and with appropriate publicity showing that doing this to the public will net a good chance of you being added to the count, I would think this sort of activity will die down.
I’m not talking of going through the nearly worthless attempt to get them jailed. The “justice system” in this country is just about useless in many ways, and the same could be said for most other nations. (I won’t say all, but that would probably be closer than “most”)
Since the perps could be almost anywhere, this would have to be a worldwide enterprise, and it is obvious that getting useful cooperation to accomplish it is a non-starter, especially if the damage is not aimed at their own country.
The definition of “sufficient” could be rather large, but yes, if given continued activity by the perps. If they practice good op-sec and only engage in the activity a few times, then perhaps not.
And, of course, it would be highly illegal. This would make crowd funding extremely difficult.
To be practical it would require international cooperation and significant changes in the law. I doubt the international cooperation would happen and I’m almost certain changes in the law to enable “hit teams” without some sort of trial would be next to impossible. And that doesn’t even take into consideration how easy it would be to frame someone for such a crime.